A television show this week reminded me of an experience from a few years ago, when I briefly met Uma Thurman at a fundraiser. Our meeting led to a stunning epiphany:

Uma, you make Jewish men feel really, really short.
A television show this week reminded me of an experience from a few years ago, when I briefly met Uma Thurman at a fundraiser. Our meeting led to a stunning epiphany:

Uma, you make Jewish men feel really, really short.
The WYSIWYG editor in WordPress 2.3 is completely borking any post I edit and half the posts I’m drafting. Bad enough bug that I would not have upgraded if I had known about this. More when I get a chance to fix this.
Yeesh. That was a pain in the ass. Site is now upgraded to WordPress 2.3 and ShadedGrey 2.0. You might note some changes to the sidebar, and other random functionality has been reworked. More changes might occur according to whim, but feel free to comment here if you approve or dislike something I’ve done.
I’m going to be mucking with the software here for a while. If anything breaks, blame the gremlins.
[W]e find that although on average all helmets attenuate invasive radio frequencies in either direction (either emanating from an outside source, or emanating from the cranium of the subject), certain frequencies are in fact greatly amplified. These amplified frequencies coincide with radio bands reserved for government use…. We speculate that the government may in fact have started the helmet craze for this reason.
I have regular debates with a friend who shall remain nameless about the nature of Mac security, after which (most of the time), I simply conclude that he and I actually live on separate but colocated planets where the computers work differently.
You know, like Earth-1 and Earth-2, Barry Allen meeting Jay Garrick.
I expect these debates will last until Doomsday, given the different facts on our respective Earths. That said, I suspect that one of the many causes of our disagreements is that we get our facts from different sources. I suspect (but really don’t know) that what he knows about the Mac comes from places that are a lot further away from the “bare metal” than mine are. (That’s one of the many advantages of hanging out with Mac developers. I’m sure the others will come to me eventually.)
So it was with some amount of glee that I read this takedown of a Business Week article by the Macalope. Maybe I don’t have the rhetorical chops to point out when mainstream tech writers are idiots. But it’s nice to know other folks do.
I was completely unable to figure out from a cursory Google search whether GrowlMail had ever been fixed for Leopard, so I spent an hour writing my own script rather than waste five more minutes seeing if it had been done before.
Added bonus: I hate seeing Growl notifications litter my screen when I’m actually staring at Mail.app, so this script does a check and only growls at you if Mail is not frontmost. I’d actually prefer it to not growl if I’m in the same Space as Mail.app, but I’m not insane enough to try coding that right now.
Code below, or download the attachment to this post. If you’re not sure how to attach an AppleScript rule to an incoming Mail message, here’s a good description.
on perform_mail_action(theData)
tell application “Mail”
set theSelectedMessages to |SelectedMessages| of theData
set theRule to |Rule| of theData
tell application “System Events” to set currApp to name of item 1 of (processes whose frontmost is true)
if currApp ? “Mail” then
repeat with a from 1 to count theSelectedMessages
do shell script “/usr/local/bin/growlnotify -a ‘Mail.app’ -m ‘” & subject of item a of theSelectedMessages & “‘ ‘” & sender of item a of theSelectedMessages & “‘”
end repeat
end if
end tell
end perform_mail_action
Attachment: DIY GrowlMail.scpt.zip
The Washington Post has a fascinating, groundbreaking article today, unfortunately buried on page A7: “McCain Mixes Up Iraqi Groups; Senator Misstates Which Extremists Are Aided by Iran.”
Perhaps I’m just jaded about the quality of journalism these days. Perhaps it’s the other articles in the paper commemorating the start of year six of the war in Iraq. But still: an article that leads with the statement, “A political leader in a position of authority made a factually incorrect statement today.” That’s revolutionary.
Compare that with the usual way that political statements are handled. Here’s the boilerplate:
[The president/chief of staff/Congressional leader] asserted something today about something important.
[S]he went on to say something else on the same topic, corroborating [his/her] first assertion.
If we do not do what [s]he wants about this issue, extremely bad things will occur.
The statements took place at [location and venue] on the occasion of [calendrical reference] to an audience of [people supporting the speaker].
[Opposition leader/representative of a nonprofit/random guy on the street] said afterwards, “no, [s]he’s wrong, that assertion has nothing to do with reality.”
[Ten paragraphs of analysis of the political implications about the statement]
So, what’s wrong with this picture? And how much better would it be if the template used was something similar to what they published on page A7 today?
[Senior official] said something today which contradicts all of the available information on the topic. [S]he repeated it several times, demonstrating that [s]he believes something in apparent opposition to what is known on the topic.
[Official’s campaign or legislative staff] did not provide any substantiating evidence to support these assertions, choosing instead to repeat the assertions using different words.
Of course, when new evidence is provided, that can certainly be the lead of the article. Likewise, when the argument is “our evidence is information that cannot be released for reasons of national security,” that could also be the lead to allow the reader to evaluate such comments themselves. And of course, statements about matters of opinion require a different structure.
But what a standard: requiring political statements to be factually accurate, or having the coverage be that the statement is wrong. I can’t help but wonder how Iraq might have gone in that case; certainly, if information opposing the invasion was available to me five years ago Friday, it was available to the newspapers.
Will we see more of this in the future? I’m not holding my breath.
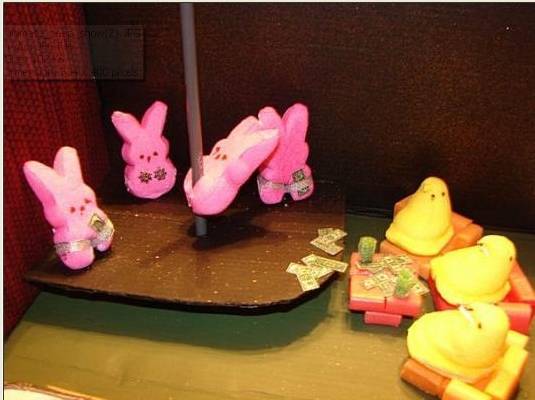
I have some very strange friends, and sometimes they email me things.
Douglas told me in the strictest confidence exactly why 42. The answer is fascinating, extraordinary and, when you think hard about it, completely obvious. Nonetheless amazing for that. Remarkable really. But sadly I cannot share it with anyone and the secret must go with me to the grave. Pity, because it explains so much beyond the books. It really does explain the secret of life, the universe, and everything.
Here’s a question. I’m spending a lot of time in Atlantic City, and so I find myself carrying around a ton of coins. Rather than carrying my own personal maracas, I dump off the change when I get home.
So what I’m wondering: what’s the optimal change to take with me in the morning to minimize this phenomenon? There’s the obvious 3 quarters, one dime, two nickels, with which you can make any amount up to a dollar. That’s fine if I’m having one retail transaction a day — but there are usually more than that.
Some mathematician must’ve found a way to make his pockets go less jingle-jangle-langle, right?
If you want to find out what the conspiracy theorists are thinking about, I happened upon a great method of monitoring them all:
Put the word conspiracy in the name of your website.
So, without further ado, a list of search terms including the word “conspiracy” that landed people here in 2007. Entries in bold showed up, like, a bazillion times. Note: don’t ask me what the hell most of these are about, I’m stumped. Triscuits?
Inspired by a post on Avish’s new blog:
Can children of mixed Jewish/Catholic marriages give up being kosher for Lent?
Cross-posting a message I wrote today for Dave Farber’s Interesting-People mailing list. The topic is regarding ISPs and their policies towards high bandwidth applications such as BitTorrent. The thread was started by Brett Glass, owner of a small ISP in Wyoming; the entire thread is archived here, while his specific message which I replied to is here.
From: Jeff Porten
Sent: Monday, February 18, 2008 1:58 PM
Subject: Re: [IP] Re: Comments on LARIAT and Comcast not same problem
On Feb 17, 2008, at 3:11 PM, Brett Glass wrote:
The default is for [BitTorrent to take up all available bandwidth]. And how many gamers, thirsting for the latest World of Warcraft update, would change that default (if they knew how)?
I’ve used over a dozen different BitTorrent clients; most of these do not expose their defaults to the users or allow the user to modify them. The ones that do clearly differ in their default settings. So your argument is provably incorrect. There is no “the default”, and I strongly suspect that if you were to download a dozen or so BitTorrent programs, you’d find that the defaults are set rather reasonably.
Secondly, in the “unprovably incorrect” category, anyone doing a casual search on “how do I use this BitTorrent thing” — which nearly everyone has to do as the software tends towards the complex — will come across many web documents that say, “do not do X, Y, or Z, as this is bad for the network.” [1] These are usually explained in terms of “ultimately bad for your download speed”, so it speaks to user self-interest rather than trying to inspire hearts and bunnies in the user.
[1]: http://www.azureuswiki.com/index.php/Good_Torrents
Alas, there is. Even if you throttle your BitTorrent client, your system (and your ISP) will be beaten on relentlessly with requests for the material. Day and night.
The largest swarms I’ve ever seen have about 40,000 members; the medians can range from 50 to 2,000 members depending upon whether you’re grabbing the latest hot release, or joining an older swarm. According to http://wiki.theory.org/BitTorrentSpecification#Messages , the messages in question are mostly measured in single-digit bitlengths [1], so presumably these require a single IP packet in each direction. The only large bandwidth requirements are in response to the request packets, which is precisely where the throttles come into play.
[1] Typo. I should have said bytelengths.
So I have difficulty with your characterization that your system is “beaten on”; it seems to me that a properly throttled BitTorrent client would be kinder to networks than, say, RSS readers and other glatt kosher network apps. Likewise, I note that iTunes podcast downloads and various network file transfers invariably max out available local bandwidth, and for some reason no one is complaining loudly about these — despite the fact that they are substantively similar to unthrottled torrents.
Long after your own download is done. And unless you “relent” by not doing P2P, you are still taking your ISP’s bandwidth for a third party.
No. If I am choosing to share a portion of my hard drive, that is a first party use of network resources, and I am the person paying the bills. If I choose to share these with anonymous third parties, that’s my choice — I happen to find it gratifying when a stranger reads my website, and resent an implication that if I don’t know my correspondent, he is somehow stealing my ISP’s resources.
The entire point is that your software cares not whether any network is “overloaded,” and seeks to bypass all of the safeguards against congestion which are part of the TCP/IP protocol suite. It is thus abusive to the network.
Actually, Brett, my particular software has rather sophisticated mechanisms to judge whether a network is busy. [1] Admittedly there are also instructions to avoid traffic shaping [2], which to my mind ranks up there with the global port 80 block that ISPs imposed on all users after Code Red was released. That said, and as you well should know, these are applications riding on top of the TCP/IP layer, not hacks to the TCP layer itself. If there is anything an end user can do to hack your TCP/IP layer, the fault is not with the clever or clueless user, the fault is with the programmer who left such glaring security holes in your routers and servers.
[1]: http://www.azureuswiki.com/index.php/ConfigAuto-Speed
[2]: http://www.azureuswiki.com/index.php/Avoid_traffic_shaping
One of the most effective P2P mitigation tactics we’ve tried is to slow down the user’s connection to compensate for the excessive duty cycle of P2P applications, keeping the net load (in gigabits per month) imposed on the network by the user down to a reasonable level. It’s the equivalent of, say, limiting the number of plates that a customer at a buffet can fill.
Yes, and this is what so profoundly angers your educated customers. We know that ISPs have always worked on the model that a few users will make high use of their connections, but the vast majority of their users will contribute high profits with low usages. This model dates back to modem banks and dial-up.
There are two ways ISPs can respond:
1) the ethical way is to say, “due to changes in our business model, we are raising our prices/changing our policies/imposing caps.” This gives their customers a chance to review their contracted relationship and decide whether to support the ISP or leave for a better competitor.
2) the unethical way is to modify their infrastructure such that they can screw over their customers in ways that they hope won’t be noticed. I happen to run a bandwidth meter in my menu bar, but ISPs very well know that most people don’t, and that ignorance is their opportunity.
As best as I can tell, ISPs to date have overwhelmingly opted for option #2. It is my opinion that the attitude of trying to put one over the ISPs is largely due to the obviously poor relationship between provider and client.
The flaw in this scheme is that it still lets abusers take bandwidth from us for the benefit of third parties, such as Blizzard and Vuze, without compensation.
Just so I’m clear — the “abusers” are people who pay you money, yes? I want to make sure that I’m understanding the terminology you’re using for your customers.
I run two businesses, and I routinely fire my underperforming customers and clients when they are more trouble than they are worth. The difference is, I do this politely, and I don’t call them names or imply that they are thieves for using the services I have promised them.
Best,
Jeff Porten
Scalzi has a great post up on how to be a thrifty writer, which counts as good advice for budding entrepreneurs as well.
One caveat: in his segue on “buy good stuff that lasts”, he mentions the epitomé of new and shiny, the MacBook Air, as its antithesis. Fact is, I own about a dozen Macs, and with the exception of a few PowerBook 140s that I bought used in 1997, they all still work. I can fire up my PowerBook Duo 210 any time I like, although its battery life is now measurable in picoseconds. The PowerBook G3 from 1999 is still in my stable of useful computers (great monitor, decent hard drive) for anything that doesn’t require heavy duty horsepower or Mac OS X 10.4 and up.
So, just saying: if you need a computer that will last for ten years, maybe you should go with the shiny.
Brian just tagged me with another blogmeme, and seeing as how I haven’t posted for a while… what the hell?
The meme in question:
1. Pick up the nearest book (of at least 123 pages).
2. Open the book to page 123.
3. Find the fifth sentence.
4. Post the next three sentences.
5. Tag five people.
What Brian didn’t realize is that he tagged me twice, so here are the top two books in the stack.
Ken Follett, Jackdaws: “The last thing Monty had said to Paul Chancellor, late on Monday night, had been: ‘If you do only one thing in this war, make sure that telephone exchange is destroyed.’ Paul had woken this morning with those words echoing in his mind. It was a simple instruction.”
Dan Harrington & Bill Robertie, Harrington on Hold ‘Em, Volume III: “The big blind has been active throughout this session, and likes to stick in a lot of small raises during a pot. The small raises don’t indicate anything about the strength of his hand. Your hand: Aâ™ A♣.”
Tried to pick up a terabyte drive from OfficeDepot.com that was listed on DealMac. To date, I’ve had the following wonderful experiences with the company:
1) Phone rep lied about expected delivery date.
2) Charge to my credit card applied three separate times ($963 for a hard drive; not exactly the bargain I was looking for).
3) Wait time of 5-7 business days before such charges can be reversed.
4) Ask for a supervisor, and get dumped into the Spanish language recordings. Unfortunately for them, I speak enough Spanish to navigate that. But a cute way of ditching problem callers.
Still on hold, so addenda to this post may apply.
Addendum 1: time on hold of sufficient length to look up executive customer service email on Consumerist, find all tracking numbers on my credit card account, compose three-paragraph email, and send. Not sure how long I’ve been on hold, but length of call is about 45 minutes. I’m now promised a callback later today….
Addendum 2: callback from executive customer service just now (5:30 PM Friday); no callback ever received from the standard escalation request. She was extremely friendly and her attitude by itself went a long way towards making me feel better about Office Depot. Summary: she could help me, but only with credit card details that I couldn’t give out to an incoming phone call. We decided to see if the problem resolves itself by Monday, otherwise I call her back.