I have great respect for the Center for Science in the Public Interest, but I’m getting tired of having them tell me, in great irrefutable detail, why I need to stop eating.
(Via The Skeptical Hypochrondiac.)
I have great respect for the Center for Science in the Public Interest, but I’m getting tired of having them tell me, in great irrefutable detail, why I need to stop eating.
(Via The Skeptical Hypochrondiac.)
CFP closed today with “Quick Takes”, a series of five-minute presentations. Bruce Schneier, the moderator, made a public call for spur-of-the-moment additions, so I took the stage to talk about something that’s been bugging me about privacy activism. I’ve already had a few people ask me to put it online, so it’s posted after the break.
I’m covering CFP 2009 for TidBITS this week. My first article went live yesterday morning; part one of my coverage should be up shortly.
If you want to follow the conference yourself, follow the links from the CFP site to the live (and archived) video coverage. It’s well worth checking out the Twitter stream; not only does it contain plenty of live comments from the conference, but the live stream is being displayed on stage and is becoming part of the conversation here. I’ll have more to say about that later — it’s an extremely interesting dynamic.
It is damned hard to attend the sessions, network in the hallways, and still find the time to write articles (and participate in that live Twitstream). There’s at least four hours of conference video, filmed in another room, that I want to watch later. It’s the proverbial drink from the proverbial firehose here.
Yes, it’s been a while since I wrote. I’ll be changing that soon. In the meantime, here’s the most amusing video I’ve seen in a long time.
A note for anyone who is Googling to see if the OS X 10.5.7 update fixes keyboard mapping problems introduced with 10.5.6 and non-US QWERTY keyboards, including using the System Events keystroke command, or various weirdnesses involving Microsoft Office:
Yes, Virginia, 10.5.7 is once again safe for your Dvorak keyboard and AppleScript macros.
tell application "TextEdit" to activate tell application "System Events" tell process "TextEdit" keystroke "testing" end tell end tell --10.5.6: y.oycbi --10.5.7: testing
Retweet Paul Krugman:
So Bobby Jindal makes fun of “volcano monitoring”, and soon afterwards Mt. Redoubt erupts. Susan Collins makes sure that funds for pandemic protection are stripped from the stimulus bill, and the swine quickly attack.
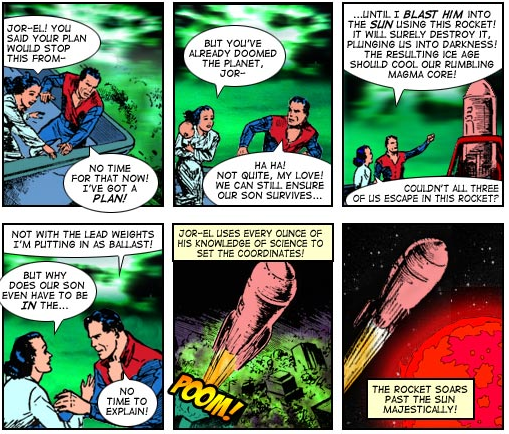
Oh, man. This Superman origin is truly awful brilliant horrible hilarious indescribable.
The scary thing is that I recognize the source artwork for 90% of the panels.
According to Boing Boing Gadgets, we’re supposed to be able to play with one of these ourselves someday soon.
Interesting story about a guy who fooled a few thousand Republicans into believing that the stimulus paid, among other things, for Laura Bush’s gambling debts and an exhumation of William H. Taft.
(Which, at $104,000, would be a bargain. The man was big.)
Tools were Twitter and a fairly simple follow strategy; personally I’m interested to see how easy it was to do.
Dear Frank,
Yes, people are mean in politics. Reality does suck.
Granted, politics have been mean, and reality has sucked, for a long time. But you’re one of the people to blame for the modern way in which it sucks, the one in which we can rebrand “torture” — and by “rebrand”, of course, I mean marketing, and not the actual red hot irons. Which you would probably call “interrogative probes.”
Not that any of us who were your students at Penn are particularly surprised. You were a great prof, but part of that was the amazing way in which you equated oleaginous stances to academic merit. “I can argue any political point so convincingly,” you said, “that none of you will be able to tell what I really believe.”
And you can. You’ve made a career of it. If you could have done so while double-dipping from the left and the right, I’m sure you would have. Some of us remember that Perot predated Gingrich on your resumé.
So have fun in Hollywood. I’m sure you’ll get along fine with the “arch-liberals” there. They’ll invite you to parties to play the foil, and you’ll go so you can pretend to be their intellectual superior. It’ll work out great for all of you.
Just do me a favor, Frank. Once you’re there, and you’re getting rich from fiction that is supposed to be fiction? Please stay. I think you’ve done the political infrastructure enough damage already.
Best,
Jeff Porten
UPenn, COL ’90
I’ll admit, the technology that Wayt Gibbs discusses in his Scientific American article on side channel attacks would be really cool, if it weren’t utterly disturbing.
The 18-point letters on the laptop screen at the end of the hall look nearly as clear as if the notebook computer were on my lap. Not only is the laptop 10 meters down the corridor, it faces away from the telescope. The image that seems so legible is a reflection off a glass teapot on a nearby table. Backes has discovered that an alarmingly wide range of objects can bounce secrets right off our screens and into an eavesdropper’s camera. Spectacles work just fine, as do coffee cups, plastic bottles, metal jewelry—even, in his most recent work, the eyeballs of the computer user.
If you save an item from your web browser, Finder’s Get Info will show you its original URL. But there’s no way to get that information as selectable text later, unless you want to do it in Terminal and know the vagaries of the mdls command. Waaaaay too complicated.
So here’s a quick script that solves that problem. Highlight any .webarchive file (or other files which have Where From information), and up pops a dialog box with that information in all its selected text goodness. (Technical details: the script gets it from mdls with flags -raw, and -name kMDItemWhereFroms. Heck, I know how to use mdls, and I think that’s too much typing.)
Download wherefrom-10.scpt.zip.

WhereFrom 1.0 by Jeff Porten is licensed under a Creative Commons Attribution 3.0 United States License.
Remember the days after 9/11, when most of us spent days furiously getting in touch with friends and family, consoling each other, and making sure everyone was alright? If you’re like most people, you look back and think, “Christ, that was tedious. I sure hope I don’t have to go through that much effort next time.”
At least, if you’re like most people, according to the developers of the Microsoft Vine social network:
Vine is a hyperlocal messaging and alert system intended to be used to share information during a crisis. Properly configured, it will gather local news and public safety announcements along with location information, reports and messages from friends–eventually even those posted to other services, like Facebook and Twitter–into a handy little dashboard. This being Microsoft (MSFT), that dashboard will be proprietary and require PCs running XP SP2 or Vista and 600 MB of hard disk space.
I’m entirely in favor of disseminating good information during a disaster. When it gets bad, common sense will let you down, and ignorance can be swiftly fatal. For example, in the event of a radiological attack, your best bet — depending on your distance from the epicenter — is to find a deep hole in the ground and stay there for a few days. But if you’re far enough away, and downwind from the attack, you should be running like hell instead.
Then, of course, you should factor in the likelihood that you’ll be running like hell down the same roads that a million other panicked citizens are using, all of you fearing death from invisible, intangible radiation poisoning. Depending on how many of your fellow citizens have guns, well, I’m thinking that should tip some folks into staying in their basements instead.
A good source of information would be crucial during this kind of emergency. And there’s your essential problem with alert networks like Vine. During normal times, no one pays attention to them. So your response is likely to have the bejesus scared out of you when they chirp up — at least until you’re desensitized to false alarms. (Which is exactly what happens with the Alert DC SMS network, and the memories many of us have from the old tests of the Emergency Broadcast System.) But no one likes to build a network and then never use it, so expect to see Vine regularly telling you about decidedly non-emergency issues, leading you to think of Vine as a broadcaster of trivia.
Meanwhile, what happens during an actual emergency? Well, if you’re using Vine, here are the necessary preconditions:
Next time I’m caught in this kind of situation, I already know what alert service I’ll use: Twitter, the alert service I use daily. Why?
Twitter’s not perfect — in the event of a national emergency, there’s no way it would scale. And it would sure be useful for it to mash up with Google Maps, GPS, and other technologies which could be lifesavers in an emergency. But in the meantime, it’ll do — and in fact, it clearly will be where people instinctively turn next time. Microsoft’s attempt to “compete” will serve only to create a cul-de-sac of people separated from the crowd, which would concern me if I weren’t convinced that Vine will be an utter failure.
Merlin Mann with a brilliant essay on priorities, and why you can have only one:
A priority is observed, not manufactured or assigned. Otherwise, it’s necessarily not a priority. You can’t “prioritize” a list of 20 tasks any more than you can “uniqueify” 20 objects by “uniqueness,” or “pregnantitze” 20 women by “pregnantness.” Each of those words means something….
It’s not a question of order or shuffling. It’s a question of brutally honest decision-making and constantly saying, “No, I have another thing to take care of.” Because, once you see what’s really there — once you know about an idea or a thing or a person or whatever that you’d reject 10,000 other things to protect and nurture — you’ve found your priority. And, consequently, you’ve discovered a bunch of other things that aren’t allowed to be priorities any more.
Sometimes, the fun part about the Internet is when it juxtaposes two stories that tell you more about the world together than either can separately.
Take my video podcast feed today:
First, an interesting argument from Alex Tabarrok at TED: demonstrating how much better the world is, post-Great Depression, than even the best economists of the 1920s could have predicted. Economic growth through globalization, he argues (and argues well), can cure the ills of any economic crisis.
Second, the Onion News Network with a report on their latest reality show, Auto Warriors, in which two factories compete against each other to see which one will survive plant closures.
Really, watch them both back-to-back.
Reading the transcript of a March 4, 2003 CNN debate about torture which is absolutely fascinating in retrospect. It opens with the question: “Following the capture of Khalid Shaikh Mohammed, the question has become whether the senior al Qaeda leader will reveal key information about the terrorist network. If he doesn’t, should he be tortured to make him tell what he knows?”
Of course, we know now that as of this interview, three days after KSM’s capture, he was probably already being tortured, based purely on the math of fitting 183 waterboardings into the remainder of March.
In favor of torture, under limited circumstances: Alan Dershowitz. Unequivocally opposed, Ken Roth of Human Rights Watch. “Moderating”: Wolf Blitzer.
Why is “moderating” in quotes? Because every one of his questions was actually more immoderate than the mostly-reasoned discussion of the interviewees:
BLITZER: Alan Dershowitz, a lot of our viewers will be surprised to hear that you think there are right times for torture. Is this one of those moments?
BLITZER: Alan, how do you know he doesn’t have that kind of ticking-bomb information right now?
BLITZER: Ken, under those kinds of rare, extreme circumstances, does Professor Dershowitz make a good point?
BLITZER: Well, let me interrupt, Ken. Let me ask you about a hypothetical case. There’s a terrorist attack. A lot of people have just been killed in New York. They capture one of the terrorists, who says, “Guess what, there’s another bomb out there, it is going to kill a lot more, but I’m not telling you where it is.”
BLITZER: Ken, let me just get back to that ticking time bomb scenario.
Go read the interview, and tell me that the man in that room most in favor of torture isn’t Wolf Blitzer.
Something came to my notice over the weekend, in the category of “the dog isn’t barking.” Despite hearing a great deal of discussion on both sides of the so-called “debate” over American use of torture, I haven’t heard anyone raise this point:
We waterboarded Khalid Sheik Mohammed 183 times in March, 2003, according to the released memos.
No one seems to have correlated that with the date we captured Khalid Sheik Mohammed — which was March 1, 2003, in Pakistan.
In other words, we started torturing that unholy bastard pretty much the minute we laid hands on him. There were no “regular interrogation methods” for him. We went straight to the Torquemada techniques.
I don’t know about you, but there seems to be an unstated presumption that when the United States does engage in torture, it’s because we need information that we can’t get any other way. KSM shows that this is clearly false; with him, we didn’t try any other way.
Actual NYT headline: Treasury Is Said to Increase Its Offer to Chrysler Lenders.
Headline I thought I read: Treasury Is Sold to Increase Its Offer to Chrysler Lenders.

Larry Lessig wanted a one-click retweet command for Twitterrific, so I wrote him one in AppleScript. And since I have no idea how to send Larry Lessig an uninvited email with an attachment without getting bitbucketed, I’ll post it here for everyone to download.
Usage: running this script will immediately retweet the selected tweet in Twitterrific, with no other UI. Period, end of story. If you don’t want to immediately retweet to all of your followers, I suggest you don’t run this script.
Lessig’s One-Click Retweet for Twitterrific 1.01

Lessig’s One-Click Retweet AppleScript by Jeff Porten is licensed under a Creative Commons Attribution 3.0 United States License.
At 11:07 AM today, CNET reported that Apple had approved the iPhone Baby Shaker application. Two hours and 18 minutes later, an update reported that the iPhone could no longer be used to simulate baby torture.
Specifically, the “game” was this:
The object of Baby Shaker is to stop the incessant crying of an infant pictured on screen by violently shaking the iPhone, at which point two red “x” marks appear over the baby’s eyes. “See how long you can endure his or her adorable cries before you just have to find a way to quiet the baby down!” reads the sales pitch for Baby Shaker.
Personally, I consider this behavior to be horrifying… on the part of Apple, that is. Because I believe that people should damn well be allowed to buy and sell this application.
Here’s the obvious argument against:
Jennipher Dickens, who founded a nonprofit organization in 2007 after her son Christopher was injured from being shaken by his father, brought the new application to our attention…. “As a mother of a child who was violently shaken at 7 weeks old, causing a severe brain injury, and the founder of a national organization for Shaken Baby Syndrome prevention, I don’t have to tell you how much this horrifies me!!!” she wrote in an e-mail.
The argument for:
If Ms. Dickens is trying to prevent shaken baby syndrome, then why is she preventing the distribution of an application that clearly demonstrates that shaking a baby can kill it?
I’ll go out on a limb and suggest that the kind of people who find this kind of thing amusing, and who share it with their amused friends, are exactly the same kind of chowderheads who, two weeks after becoming an unplanned parent, might inflict devastating injuries on their child through sheer ignorance.
Much better to ban a tasteless joke, and shut down any possibility of viral information-sharing. Just so long as no one is offended, which is the important thing.